Who’s Responsible for IoT Security? (Part 3 of 3)
In Part 1 of this blog series, we talked about why updates matter and the security gap between what consumers expect and what IoT devices…

In Part 1 of this blog series, we talked about why updates matter and the security gap between what consumers expect and what IoT devices…

In Part 1 of this blog series, we looked at why IoT device updates matter, why some devices can’t be updated at all, and how…

Smart homes are no longer futuristic. Doorbells talk to phones. Thermostats learn your schedule. Lights respond to voice commands. Refrigerators send alerts. All of these…

Artificial Intelligence (AI) is beginning to reshape certification processes from job analysis and test development to exam health checks. While these tools offer speed and…

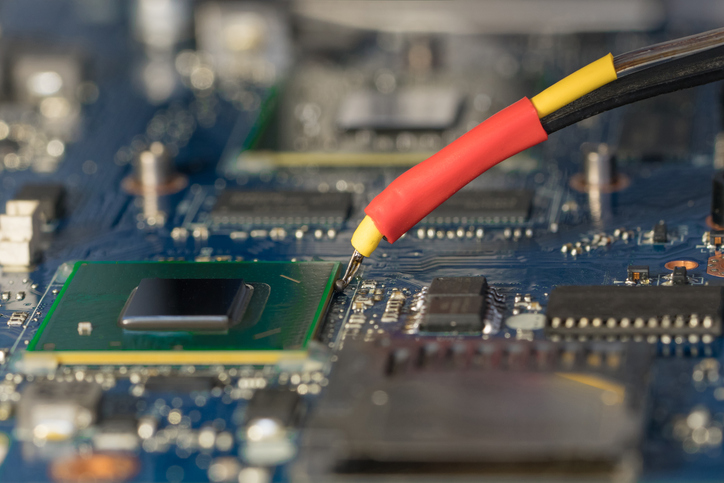
President Biden issued Executive Order 14028, Improving the Nation’s Cybersecurity, on May 12, 2021 to address “persistent and increasingly sophisticated malicious cyber campaigns that threaten…
When two dissimilar metals are joined at two junctions, they generate what is known as an electromotive force (emf). This emf arises due to varying…

Two systems of weights and measures are derived from English Units: the US Customary System and the British Imperial System. Neither is dominant worldwide, but…

Role based access control (RBAC) is an approach in computer systems security in which each user is assigned one or more roles, and each role…

The Smart Grid is a collection of technologies, all communicating and interacting with each other, grid operators, producers, and consumers. Utilizing the existing infrastructure and…